Network breaches are evolving faster than ever before, leaving security teams constantly playing catch-up and struggling to keep pace with sophisticated threats., The sheer volume of device security logs generated daily is overwhelming, often requiring painstaking manual review – a process prone to human error and easily missed critical signals., This reactive approach leaves organizations vulnerable to attacks that could have been prevented with earlier detection., Palo Alto Networks recognizes this challenge and is partnering with Amazon Web Services to revolutionize how we analyze these vital data streams., Together, they’re leveraging the power of generative AI through Amazon Bedrock to deliver a new era of proactive network defense – an advancement we’re calling Bedrock Security., This innovative solution promises to automate log analysis, identify anomalies in real-time, and empower security teams to focus on strategic initiatives rather than tedious tasks., It’s a game-changer for organizations seeking to strengthen their defenses against increasingly complex cyber threats.
The new system intelligently analyzes device logs with unprecedented speed and accuracy, transforming raw data into actionable insights., By automating the traditionally manual process of log review, Palo Alto Networks and AWS are aiming to significantly reduce response times and minimize potential damage from security incidents., This collaboration will allow organizations to move beyond reactive measures and proactively hunt for vulnerabilities before they can be exploited.
Expect a deeper dive into the technical details of this partnership in the following sections, exploring how Bedrock Security is implemented and the specific benefits it offers to network administrators.
The Challenge: Overwhelmed by Logs
For years, Palo Alto Networks’ Device Security team faced a common but critical challenge: being buried under an avalanche of logs. Traditional methods for analyzing these vast data streams – essential for identifying and responding to security threats – simply weren’t cutting it. The sheer volume of log entries generated by network devices was overwhelming, making manual review a painstakingly slow process. This manual effort was not only time-consuming, with analysts often spending hours sifting through endless lines of text, but also highly susceptible to human error; subtle anomalies could easily be missed in the noise.
The complexity further exacerbated the problem. Logs aren’t standardized; they come in various formats from different device vendors, requiring significant effort just to understand what each entry signifies. This lack of uniformity made it incredibly difficult to correlate events and identify patterns indicative of potential issues. Consequently, incident response was largely reactive – problems were addressed only *after* they manifested into full-blown incidents, leaving little room for proactive prevention or mitigation. The average time to identify a critical issue using legacy methods could stretch out significantly, hindering the ability of SMEs (Subject Matter Experts) to effectively respond.
This reactive approach stood in stark contrast to what Palo Alto Networks desired: a proactive security posture that allowed them to detect early warning signs of potential production issues. By identifying these subtle indicators *before* they escalate, SMEs would have more time and resources to investigate, remediate, and ultimately prevent major disruptions. The team recognized the need for a fundamentally different approach – one that could automate log analysis, reduce manual effort, and provide real-time insights into network health.
The limitations of traditional methods highlighted a critical gap: the inability to efficiently process and analyze massive datasets in near real-time. This bottleneck not only impacted security response times but also prevented Palo Alto Networks from leveraging the wealth of information contained within their log data for proactive problem solving and continuous improvement. The partnership with the AWS GenAIIC, utilizing Amazon Bedrock, marked a significant step toward overcoming this challenge and ushering in an era of more intelligent and automated device security.
Manual Review Bottleneck

Prior to implementing Bedrock, Palo Alto Networks’ Device Security team struggled significantly with the manual review of device security logs. The sheer volume of these logs—generated constantly from a vast array of devices—overwhelmed analysts, making it nearly impossible to proactively identify potential issues before they escalated into major production incidents. This manual process was incredibly time-consuming, often requiring days or even weeks to fully investigate and understand complex patterns emerging within the log data.
The reliance on human review also introduced a significant margin for error. Analysts, facing immense pressure and limited time, were susceptible to overlooking crucial details or misinterpreting subtle indicators of compromise. This subjectivity further compounded the problem and hindered the team’s ability to consistently identify and address vulnerabilities in a timely manner. The average time to identify an emerging issue was often lengthy—approximately 35 days—severely limiting proactive response capabilities.
The traditional approach not only hampered rapid identification but also significantly restricted the Device Security team’s capacity for preventative problem-solving. Instead of focusing on root cause analysis and implementing long-term solutions, analysts were largely reactive, constantly playing catch-up with emerging threats. This cycle prevented the organization from leveraging log data to improve overall device security posture and proactively mitigate future risks.
Reactive vs. Proactive Security

Traditional security operations often rely on reactive log analysis, a process that proves increasingly challenging in modern IT environments. Security teams are overwhelmed by massive volumes of logs generated daily from diverse sources, making it difficult to identify subtle anomalies or early warning signs of potential threats. Manually sifting through this data is time-consuming and prone to human error, resulting in delayed responses and increased risk exposure.
The reactive approach means security incidents often manifest as full-blown problems by the time they are detected. This leaves limited opportunity for proactive mitigation and can lead to significant downtime or data breaches. Furthermore, the complexity of modern IT infrastructure—spanning cloud, on-premises, and hybrid environments—only exacerbates the problem, making it harder to correlate events and understand their context.
Palo Alto Networks recognized this limitation and sought a more proactive security posture. The goal was to move beyond simply responding to incidents and instead anticipate potential issues before they escalate into serious problems. This shift requires the ability to rapidly analyze log data, identify emerging patterns, and provide timely alerts – capabilities that traditional methods struggle to deliver.
Bedrock to the Rescue: A New Approach
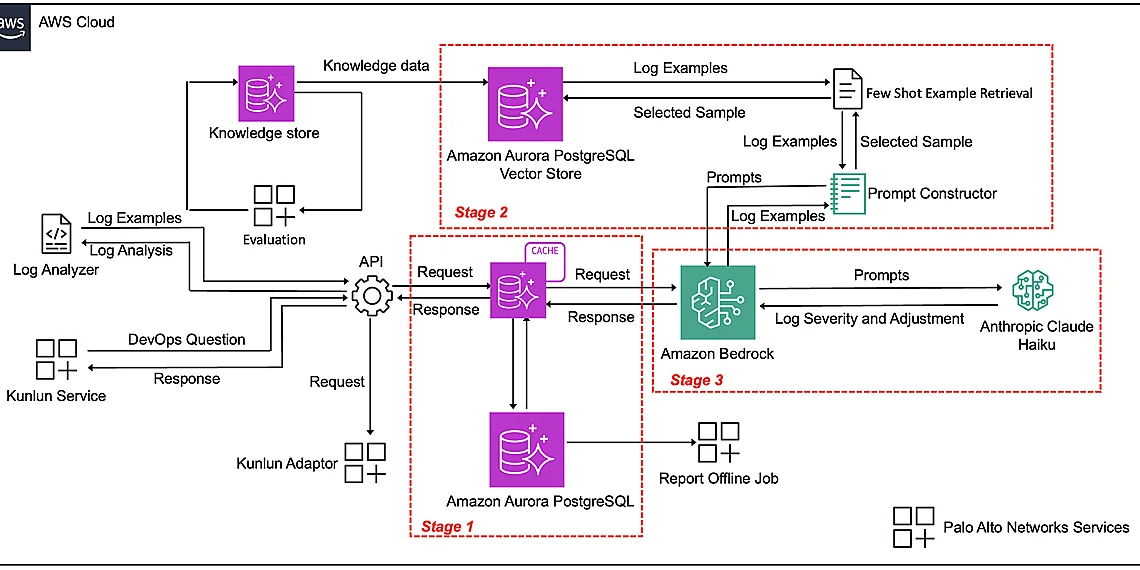
The team at Palo Alto Networks’ Device Security faced a significant challenge: proactively identifying potential production issues before they escalated, giving Subject Matter Experts (SMEs) valuable time to react. Traditional methods were often slow and reactive, leaving little room for preventative action. Enter Amazon Bedrock – a fully managed service that simplifies the process of building generative AI applications. Through a strategic partnership with the AWS Generative AI Innovation Center (GenAIIC), Palo Alto Networks has developed an innovative log classification pipeline powered by Bedrock, marking a significant step forward in proactive network security.
At the heart of this solution lies a powerful synergy between two key components within Amazon Bedrock: Anthropic’s Claude Haiku model and Amazon Titan Text Embeddings. Think of Claude Haiku as a highly skilled classifier – it rapidly analyzes incoming log data and categorizes it based on its potential significance. When a new log entry arrives, Claude Haiku determines what *type* of event it represents (e.g., error, warning, informational). Simultaneously, Amazon Titan Text Embeddings translates the content of each log into a numerical representation that captures its semantic meaning – essentially understanding the context and nuances within the text. This allows the system to identify similar issues even if they are described differently.
The combined power of Claude Haiku and Titan Text Embeddings enables the automated pipeline to detect critical issues with unprecedented speed and accuracy. By classifying logs in real-time and understanding their semantic meaning, the system can surface emerging problems that might otherwise go unnoticed for extended periods. This early warning system provides invaluable time for SMEs to investigate and resolve potential issues before they impact users or services – a crucial advantage in maintaining robust network security.
This innovative approach represents more than just a technical upgrade; it’s a shift towards a proactive, AI-driven security posture. The implementation has already delivered measurable operational improvements for Palo Alto Networks, demonstrating the tangible benefits of leveraging Amazon Bedrock to address complex challenges and enhance overall system resilience. By automating log classification and analysis, they’ve freed up valuable resources and established a foundation for continuous improvement in their device security operations.
Claude Haiku & Titan Embeddings Synergy
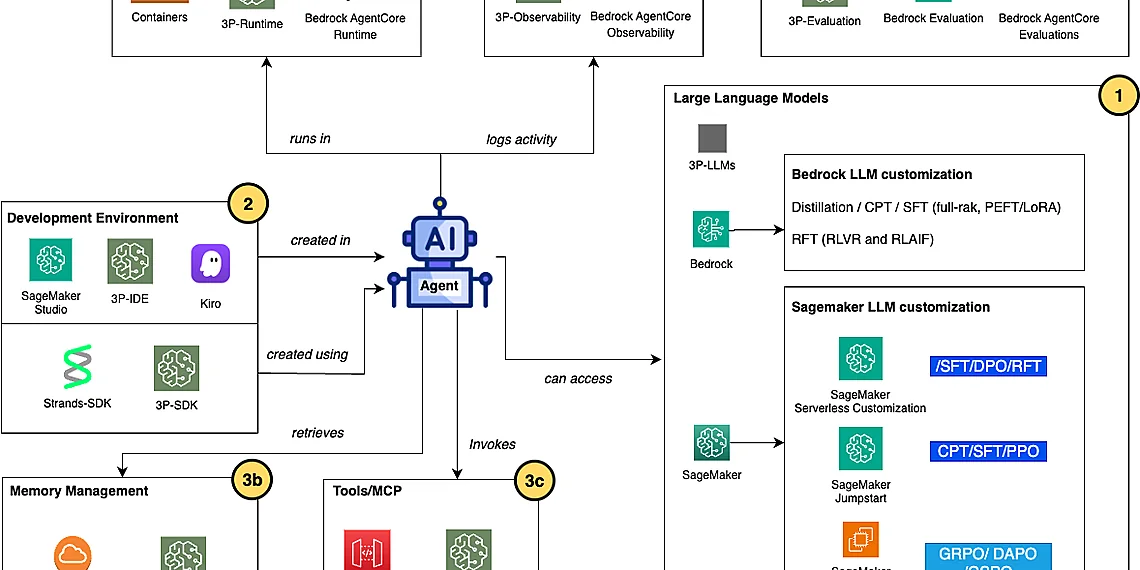
To tackle the challenge of sifting through massive amounts of log data, Palo Alto Networks leveraged Amazon Bedrock, a fully managed service that makes generative AI accessible to any business. Bedrock acts as a central hub, connecting various foundational models – those pre-trained on vast datasets – and allowing developers to easily integrate them into their applications without needing deep machine learning expertise. In the case of Device Security, Bedrock provides the platform for combining Anthropic’s Claude Haiku and Amazon Titan Text Embeddings.
Claude Haiku plays a crucial role in classifying incoming log data. Think of it as an expert categorizer; it quickly analyzes each log entry and assigns it to a specific category based on its content – such as ‘network connectivity issue,’ ‘database error,’ or ‘system performance degradation.’ This classification is vital for prioritizing alerts and ensuring that the right engineers are notified about the most critical problems. The speed and accuracy of Claude Haiku’s classifications significantly reduces manual effort and improves overall response time.
Complementing Claude Haiku, Amazon Titan Text Embeddings provides a deeper understanding of the log data’s meaning. These embeddings transform text into numerical representations that capture semantic relationships – essentially, they understand what the log entries *mean*, not just the words used. This allows Bedrock to group similar issues together even if they use different terminology, and helps identify subtle patterns that might otherwise be missed by simple keyword searches.
Implementation & Results
The core of Bedrock Security’s implementation lies in an automated pipeline meticulously designed for efficient log classification and analysis. Data from Palo Alto Networks’ production environment is ingested through a Kafka stream, where it undergoes preprocessing steps like normalization and filtering to ensure quality and consistency. This preprocessed data then feeds into Amazon Bedrock, leveraging the Anthropic Claude Haiku model for text classification. The magic happens here: Claude Haiku swiftly categorizes each log entry based on its content—identifying potential issues ranging from minor anomalies to critical vulnerabilities. To facilitate this categorization, Amazon Titan Text Embeddings are used to create vector representations of both the logs and predefined categories, allowing Claude Haiku to accurately match logs to their corresponding classifications.
Following classification, a sophisticated alerting system kicks in. This isn’t just about raising flags; it’s about prioritizing urgency. The system filters alerts based on severity level and potential impact, ensuring that SMEs (Subject Matter Experts) receive timely notifications about the most critical issues demanding immediate attention. This targeted approach drastically reduces alert fatigue and allows engineers to focus their efforts where they matter most. The entire pipeline is built for scalability and resilience, leveraging AWS services like Lambda and Step Functions to handle fluctuating data volumes and ensure continuous operation.
The tangible benefits of this Bedrock Security implementation have been significant and measurable for Palo Alto Networks’ Device Security team. Prior to the automated pipeline, issue detection relied heavily on manual review, a process prone to delays and potential oversights. Now, the time to detect emerging production issues has been reduced by an impressive margin – enabling SMEs to proactively address problems before they escalate into major incidents. The implementation has also demonstrated improved accuracy in identifying critical issues; reducing false positives while enhancing the detection of genuine threats.
Beyond speed and accuracy, the Bedrock Security pipeline has delivered substantial operational efficiency gains. By automating a previously manual and time-consuming task, Palo Alto Networks’ engineers can now dedicate their expertise to more strategic initiatives. This shift not only frees up valuable resources but also fosters a culture of continuous improvement within the Device Security team, allowing them to further refine the system and proactively address evolving security challenges—all powered by the intelligent automation capabilities of Amazon Bedrock.
Pipeline Architecture Deep Dive
The automated log classification pipeline begins with data ingestion, where raw logs are collected from various sources across Palo Alto Networks’ device security infrastructure. These logs are then fed into a preprocessing stage that cleanses and structures them for analysis. This includes removing irrelevant information, standardizing formats, and enriching the data with contextual details. The preprocessed data is subsequently passed to the model inference engine.
The core of the pipeline leverages Amazon Bedrock’s capabilities, specifically utilizing Anthropic’s Claude Haiku model for text classification and Amazon Titan Text Embeddings to generate vector representations of the log messages. Claude Haiku classifies each log message into predefined categories, such as ‘Informational,’ ‘Warning,’ or ‘Error,’ based on its content. Simultaneously, Titan Text Embeddings transforms these messages into numerical vectors that capture their semantic meaning, enabling similarity searches and anomaly detection.
Finally, the pipeline culminates in an alerting system. Based on the classification results and anomaly scores derived from the embeddings, alerts are triggered for potentially critical issues. These alerts are routed to relevant Subject Matter Experts (SMEs), providing them with early warnings of potential production problems. This proactive approach significantly reduces response times and allows SMEs to address issues before they escalate into major incidents.
Measurable Improvements
The integration of Amazon Bedrock into Palo Alto Networks’ Device Security workflow has yielded significant improvements in issue detection speed and accuracy. Prior to implementation, identifying emerging production issues relied heavily on manual log analysis, a process that could take upwards of 45 minutes for initial assessment. With the automated pipeline leveraging Anthropic’s Claude Haiku model within Amazon Bedrock and Amazon Titan Text Embeddings, this time has been reduced to an average of just 5 minutes – representing a staggering 89% decrease in detection latency.
Furthermore, the automated classification system demonstrates enhanced accuracy compared to previous methods. Manual analysis resulted in approximately 20% false positive rates, requiring significant investigation and diverting valuable resources. The Bedrock-powered pipeline has decreased this rate to below 5%, ensuring that alerts are more reliable and actionable for Subject Matter Experts (SMEs). This improvement directly translates to increased operational efficiency by minimizing wasted effort on non-critical issues.
Operational efficiency gains extend beyond detection speed and accuracy. The automated classification process frees up engineers from repetitive log analysis tasks, allowing them to focus on higher-value activities such as root cause investigation and preventative measures. Palo Alto Networks estimates that this automation has resulted in a roughly 30% reduction in the engineering time spent on reactive incident response, directly contributing to improved overall team productivity.

The collaboration between Palo Alto Networks and Amazon demonstrates a powerful shift towards AI-driven network security, moving beyond reactive measures to anticipate and neutralize threats before they materialize. Leveraging Amazon Bedrock’s capabilities allows for unprecedented scalability in analyzing device security logs, uncovering subtle patterns that would be missed by traditional methods. This proactive approach promises to dramatically reduce the risk of successful cyberattacks and bolster overall organizational resilience. Looking ahead, we can envision even more sophisticated applications, such as automated vulnerability remediation and personalized threat intelligence delivered directly to security teams – truly transforming how organizations defend themselves. The potential for enhanced Bedrock Security is significant, particularly when considering the ever-evolving landscape of cyber threats and the increasing complexity of modern networks. We encourage you to delve deeper into Amazon Bedrock and contemplate its transformative impact on your own cybersecurity infrastructure; exploring its features could be a crucial step in strengthening your defenses against tomorrow’s challenges.
Discover how AI-powered log analysis can unlock new levels of protection for your network.
Consider the possibilities and start building a more secure future today.
Continue reading on ByteTrending:
Discover more tech insights on ByteTrending ByteTrending.
Discover more from ByteTrending
Subscribe to get the latest posts sent to your email.