Inside the G1 Security Breach
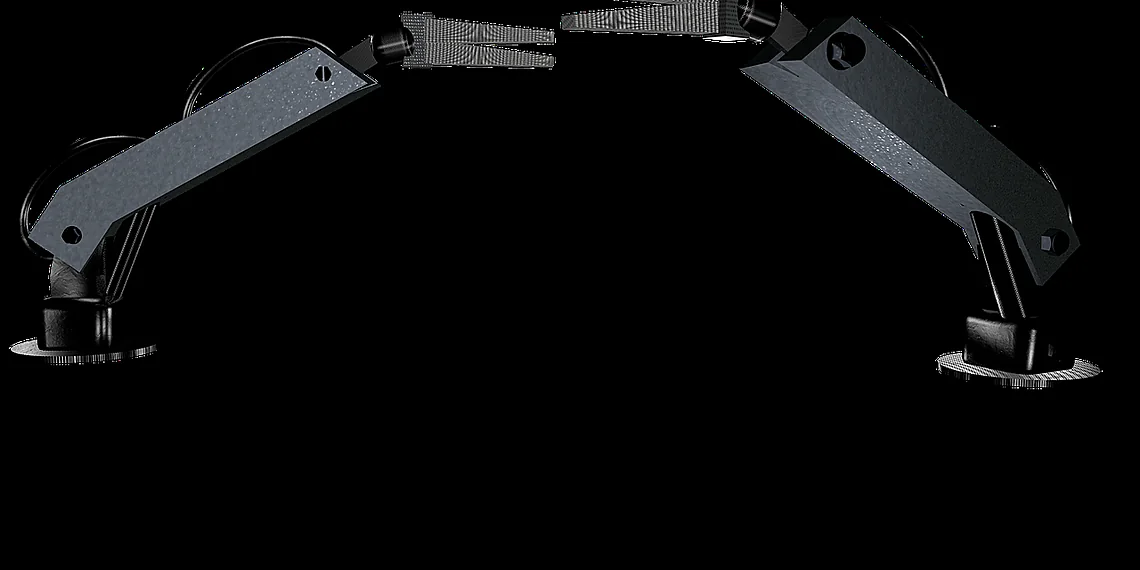
New findings from a team of international security researchers have exposed alarming vulnerabilities within the increasingly popular Unitree G1 humanoid robot. These flaws, according to the report, indicate that data collected by these robots could be secretly transmitted to servers in China and that the devices are susceptible to relatively simple hacking attempts. Consequently, concerns regarding privacy and potential misuse have arisen.
The Unitree G1 has rapidly gained traction across various sectors including research labs, manufacturing facilities, and even some law enforcement agencies. Its affordability and capabilities have made it an attractive option for automation needs; however, these recent discoveries cast a long shadow over its widespread adoption. Therefore, careful consideration must be given to the security implications of deploying humanoid robots.
How the Exploits Work
The security researchers detailed several critical vulnerabilities. One major concern revolves around data transmission. The G1 humanoid robot collects substantial amounts of data including video feeds, audio recordings, and sensor readings during operation. The investigation revealed that this data is not adequately encrypted and can be routed through servers located in China without the user’s knowledge or consent; as a result, sensitive information could be exposed.
// Example vulnerability code snippet (Illustrative only)
- Unencrypted network traffic
- Default credentials
Furthermore, gaining control of a G1 robot is surprisingly straightforward. The team demonstrated that using commonly available tools and basic hacking techniques, they could remotely access the robot’s systems, manipulate its movements, and even extract sensitive data. The robots rely on default passwords in some instances, making them easy targets for malicious actors; therefore, immediate action is needed to mitigate this risk.
Covert Surveillance Concerns
The implications of these vulnerabilities extend beyond simple data breaches. Imagine a scenario where multiple G1 robots are deployed within a facility or public space. A compromised robot could be used to perform covert surveillance, gathering intelligence and relaying it back to an external party – potentially even a hostile nation-state. This highlights the potential for misuse of humanoid robots in sensitive environments.
Potential Cyberattack Risks
Beyond the immediate privacy concerns, researchers warn that these robots could become vectors for larger cyberattacks. A compromised G1 robot connected to a local network could provide a backdoor into more sensitive systems, enabling attackers to steal data or disrupt operations. The interconnected nature of modern networks means that even seemingly isolated devices like humanoid robots can pose significant risks; notably, this risk increases with the growing integration of robotics in various industries.
“These findings highlight the critical need for robust security measures in robotics,” stated Dr. Anya Sharma, lead researcher on the project. “Manufacturers and users alike must prioritize cybersecurity to prevent these powerful tools from being exploited.”
Mitigation Strategies
- Change default passwords immediately
- Implement strong network segmentation
- Regularly update robot firmware
- Encrypt all data transmitted by the robots

Conclusion
The revelations regarding the Unitree G1 robot’s vulnerabilities are a stark reminder that technological advancement must be accompanied by rigorous security considerations. While these robots offer exciting possibilities for automation and innovation, their potential for misuse cannot be ignored. Addressing these flaws is paramount to ensuring the safe and responsible deployment of humanoid robot technology in the future; furthermore, ongoing vigilance and proactive security measures are essential.
Source: Read the original article here.
Discover more tech insights on ByteTrending.
Discover more from ByteTrending
Subscribe to get the latest posts sent to your email.