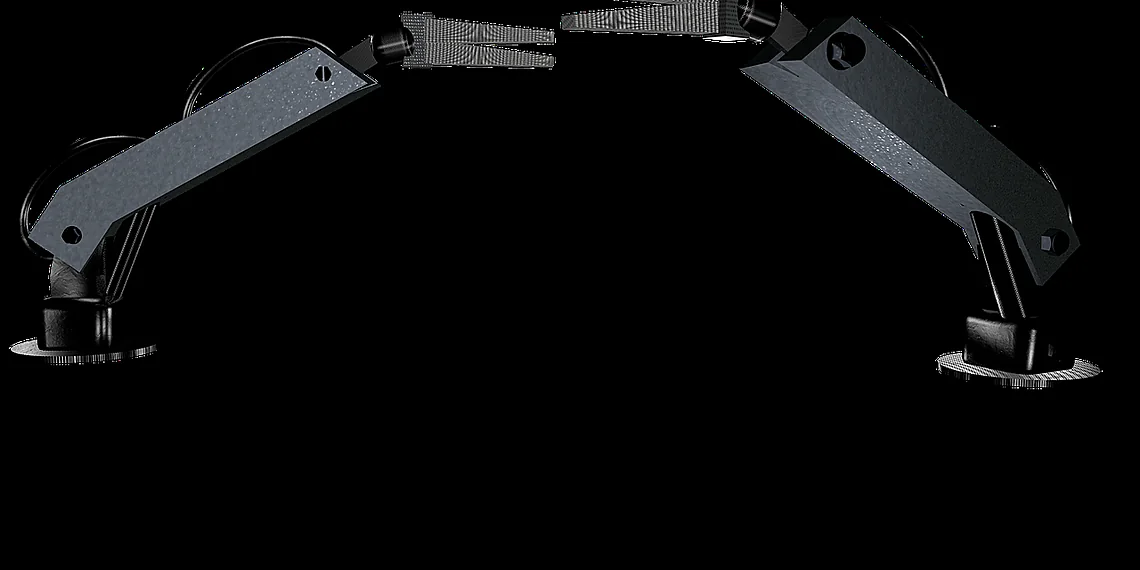
The burgeoning field of robotics brings incredible advancements, but also introduces new security challenges. Recently, a critical Unitree robot exploit was revealed, highlighting vulnerabilities in the popular quadruped and humanoid robots. These machines, including the Go2 and B2 quadrupeds and G1 and H1 humanoids, are susceptible to unauthorized access through a flaw within their Bluetooth Low Energy (BLE) Wi-Fi configuration interface. Understanding this Unitree robot exploit is crucial for developers, users, and anyone interested in robotics security.
Understanding the Unitree Vulnerability and its Impact
The vulnerability stems from a weakness in the BLE Wi-Fi setup process utilized by several Unitree robots. This allows malicious actors to potentially gain root access, effectively taking complete control of the device. Consequently, this compromise can lead to data breaches, system manipulation, and even physical harm if the robot is performing tasks involving human interaction. Furthermore, the ease with which an attacker can exploit this vulnerability underscores the need for improved security protocols within these robotic platforms.
The Role of BLE in Unitree Robot Configuration
BLE simplifies the initial Wi-Fi setup process for Unitree robots by providing a wireless connection option. However, as researchers have demonstrated with UniPwn, this convenience comes at a cost if security measures are not robustly implemented. Consequently, the design choice of using BLE has created an attack vector that can be exploited by those with malicious intent.
The Scope of Affected Unitree Models
Initially discovered and detailed in a public disclosure on September 20th, the vulnerability impacts several popular Unitree robot models. Specifically, the Go2 and B2 quadrupeds, along with the G1 and H1 humanoids, are all considered vulnerable. Therefore, users of these devices should take immediate steps to mitigate the risk as detailed later in this article.
How the Exploit – UniPwn – Works
The exploit, dubbed “UniPwn,” exploits several security lapses present in the Unitree robot firmware. The researchers Andreas Makris and Kevin Finisterre uncovered that hardcoded encryption keys are used during authentication, enabling unauthorized users to gain access simply by encrypting the string ‘unitree.’ For example, this bypasses standard authentication procedures. Subsequently, attackers can inject malicious code disguised as legitimate Wi-Fi credentials, granting them root privileges on the compromised robot.
The Hardcoded Encryption Key Issue
One of the most concerning aspects of this Unitree robot exploit is the reliance on hardcoded encryption keys. These keys should be unique and regularly updated; however, their presence in the firmware makes exploitation significantly easier for those with malicious intentions. Therefore, Unitree’s decision to use such a simple and predictable key poses a significant security risk.
The Injection of Malicious Code
Once authentication is bypassed, attackers can inject malicious code directly into the Unitree robot‘s system. This code then executes with root privileges, giving the attacker complete control over the device’s functionality and data. Notably, this ability to execute arbitrary code makes the potential damage from exploitation significantly more severe.
The Wormable Threat: A Cascade of Compromises
What truly elevates the severity of this vulnerability is its wormable nature. An infected Unitree robot can actively scan for other vulnerable devices within BLE range and automatically compromise them, creating a potential botnet without any user intervention. As a result, a single compromised device could rapidly spread the exploit to numerous others, amplifying the impact exponentially. This capability demands immediate action to prevent widespread infection.
Mitigation Strategies and Responsible Disclosure
Following initial discovery in May of 2025, researchers attempted to communicate with Unitree about the vulnerability but received minimal progress. Consequently, they publicly disclosed details through UniPwn due to a lack of response, highlighting a concerning pattern of security neglect. To protect your robots, isolate vulnerable models on separate Wi-Fi networks and disable Bluetooth connectivity as immediate steps. For the long term, proactive measures from Unitree are vital.

The Unitree robot exploit serves as a stark reminder of the growing importance of cybersecurity in robotics. As robotic technology becomes increasingly integrated into our lives, ensuring its security is paramount to maintaining trust and preventing misuse. Furthermore, ongoing discussions regarding these vulnerabilities will be featured at an upcoming Cybersecurity for Humanoids workshop.
Source: Read the original article here.
Discover more tech insights on ByteTrending.
Discover more from ByteTrending
Subscribe to get the latest posts sent to your email.