The Looming Threat of Quantum Computers and the Need for Post-Quantum Cryptography
The world’s reliance on cryptography is facing an unprecedented challenge: the impending arrival of powerful quantum computers. These machines, harnessing the principles of quantum mechanics, possess the potential to fundamentally alter our understanding of computation and, critically, break the cryptographic algorithms that secure our digital lives. The National Institute of Standard and Technology (NIST) has responded with a pivotal step – the publication of the first official standard for post-quantum cryptography (PQC) algorithms in 2022, driven by a Biden administration memorandum mandating federal agency transitions by 2035. This shift underscores the urgent need to understand **post-quantum cryptography** and its role in safeguarding information against this evolving threat. The adoption of these new methods is vital for maintaining data security in a future where existing systems become vulnerable.
Understanding Traditional Cryptography and Its Vulnerabilities
Traditional cryptographic methods, such as RSA and elliptic curve cryptography, rely on mathematical problems that are incredibly difficult to solve using classical computers. These algorithms operate by generating secret keys used for encryption and decryption. The security of these systems hinges on the assumption that it would take a quantum computer an impractical amount of time to break these calculations. However, quantum computers utilize quantum mechanics to perform computations in ways fundamentally different from classical computers. Specifically, they exploit phenomena like superposition and entanglement to tackle complex mathematical problems exponentially faster than any traditional machine. As quantum computing technology advances, particularly with the development of sufficiently powerful quantum computers, the security of RSA and ECC will be severely compromised; therefore, the shift to **post-quantum cryptography** is no longer a future consideration but an immediate necessity.
| Algorithm Type | Key Size (approx.) | Security Level (estimated) | Performance Characteristics |
|---|---|---|---|
| RSA | 2048-4096 bits | Moderate – Vulnerable to Shor’s Algorithm | Fast for encryption and decryption |
| ECC (Elliptic Curve Cryptography) | 256-384 bits | Moderate – Vulnerable to Shor’s Algorithm | Lower computational overhead than RSA |
| CRYSTALS-Kyber (PQC Standard) | 2048 bits | High | Relatively fast performance, well-suited for key exchange |
| Falcon (PQC Candidate) | 2192 bits | High | Good performance in constrained environments |
The core concept behind **post-quantum cryptography** is the development of cryptographic algorithms that are resistant to attacks from both classical and quantum computers. These new algorithms rely on mathematical problems believed to be equally difficult for both types of machines, providing a robust defense against potential quantum threats. Furthermore, NIST’s selection process has focused on algorithms based on lattices, codes, multivariate equations, and hash-based signatures – approaches that are considered more resilient to quantum attacks than existing methods. The transition represents a significant undertaking, demanding fundamental changes across numerous sectors.
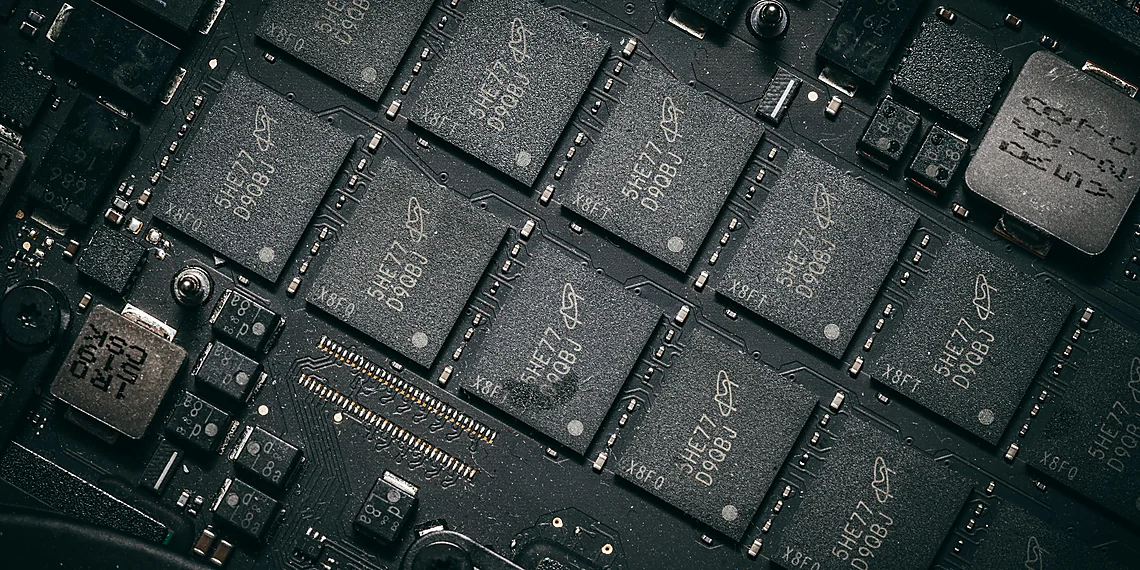
With the mathematics behind PQC ironed out, and standards in hand, the work of adoption is now underway. This is no easy feat: every computer, laptop, smartphone, self-driving car, or IoT device will have to fundamentally change the way they run cryptography. Ali El Kaafarani, a research fellow at the Oxford Mathematical Institute who contributed to the development of NIST’s PQC standards, and founder of PQShield, spoke with IEEE Spectrum about how adoption is going and whether the new standards will be implemented in time to beat the looming threat. He highlighted that the shift isn’t just about technical changes; it’s a compliance issue fueled by government mandates and deadlines.
Initially, many questioned “When will we have a quantum computer?” But in 2015, the risk was categorized as real, prompting a shift in focus from ‘why’ to ‘how.’ The supply chain now actively seeks solutions, ranging from chip design to network security layers and critical national infrastructure, aiming to build a post-quantum-enabled network security kit. This proactive approach is essential for mitigating the potential disruption caused by quantum computing.
Challenges and Considerations in Implementing Post-Quantum Cryptography
El Kaafarani explained that while the math is solid, implementing it presents significant challenges. The transition impacts everything from small sensors to large servers, creating diverse security requirements and energy consumption considerations. This isn’t a purely mathematical problem; it’s an implementation challenge requiring specialized expertise. Furthermore, the deployment of PQC algorithms introduces new complexities related to key management, certificate validation, and compatibility with existing systems. The sheer scale of this transition demands careful planning and execution.
Cryptography is often overlooked until it breaks down. Enterprises typically use it when forced by regulations. Now, the issue is much bigger as companies are being told to change existing cryptography that has been used for 15-20 years. This necessitates a shift in mindset – moving beyond reactive security measures and embracing proactive strategies for mitigating quantum risks. The timeline for widespread adoption remains uncertain, but the potential consequences of inaction are too significant to ignore.
El Kaafarani emphasized the newness of PQC and the potential for previously unseen attack vectors. He noted that attackers are exploring side-channel attacks – exploiting energy consumption or timing variations – to extract keys. Because PQC is relatively untested at scale, there’s a risk of vulnerabilities emerging. PQShield employs vulnerability teams to proactively test their designs, anticipating potential threats. This ongoing vigilance is crucial for ensuring the long-term security of **post-quantum cryptography** systems.
El Kaafarani acknowledged that adoption has been uneven. While many companies are making significant progress and integrating PQC into new products, others are lagging behind due to a lack of awareness or prioritization. He believes that most infrastructure will be post-quantum secure by 2035, but emphasized the ongoing need for vigilance and continuous security testing.
He highlighted the importance of proactive engagement from supply chain stakeholders – urging them to influence their suppliers’ requirements and timelines. The ultimate goal is a robust and resilient network security ecosystem capable of withstanding future quantum threats. Ultimately, the successful adoption of **post-quantum cryptography** will depend on collaboration across industries, governments, and research institutions.
Source: Read the original article here.
Discover more tech insights on ByteTrending.
Discover more from ByteTrending
Subscribe to get the latest posts sent to your email.